Time and again, the prior art searches we conduct teach us new lessons. These lessons not only help us add new rules to our little black book of prior art searching but also point us to the true north. They teach us that possibilities are unlimited and we will eventually find what we are looking for.
An invalidation search that we conducted recently for one of our regular clients, taught us another valuable lesson: “A Prior art search is way more than just providing references.”
As a first step, which followed after an initiation email, I developed my understanding of the patent. It disclosed a concept of handover (in idle mode) from LTE (4G) to 3G/2G network.
I found that the technology was all about moving from a 4G network area to 3G/2G area, wherein the routing area update is sent from a user device to a new/target SGSN (Serving GPRS Support Node). The target SGSN upon receiving the update sends a PDP(Packet Data Protocol) context request to MME (Mobility Management Entity) in 4G network for obtaining security capabilities like authentication keys of a user.
The MME upon receiving the PDP request derives various keys e.g. encryption key, integrity protection key, et cetera, using a root key, and sends them along with security capabilities of the user to a new SGSN, making the new SGSN capable of providing user services.
The concept of deriving these various security keys using a root key at MME was the most important aspect of the patent.
We’ve observed that in the case of patents depicting specific industry-accepted components related to the communication domain, searching in standards helps to get new leads as well as understand various aspects of the concept in a better manner. And in the past, we have invalidated patents using standards.
That said, we started with the standard search on 3GPP and ETSI. As we were expecting, we found the concept was existing in the case of intra-system handover – where the MME (in a 4G network) sends a request to HSS in order to derive the keys.
After finding the concept to be in existence for intra-system handover, we embarked to find the same for inter-system handover as it was required to invalidate the patent in question. We checked change requests submitted by the same company, for that matter.
We found no references, however. Almost every reference was discussing the same concept of a derivation of keys at MME in light of 4G to 2G/3G handover. It was time to change the gear and shift the focus back to the patents.
In the beginning, we came across references disclosing the concept of deriving authentication keys at MME. Unfortunately, we didn’t find a single reference disclosing anything related to handover. For example, we found a reference (let’s say Patent A) disclosing the concept of RAU (Routing Area Update) update being sent from the user device to new SGSN, which further sends a corresponding context request to MME. However, the concept of sending security capabilities and derivation of security keys using a root key by MME (upon receiving context request) was not explicitly mentioned in these references.
Locating that important concept was still a challenge. We were still in the hunt for finding more references. It was time to shift the gears again. This time, we shifted our focus to references discussing the functionality of MME during any intra-RAT/internetworking handover.
Bingo! We found a reference (Patent B) disclosing the concept of inter-system handover from LTE to WiMAX. Although it did not disclose LTE to 3G/2G handover, it disclosed the concept of deriving security-related keys at MME using a root key.
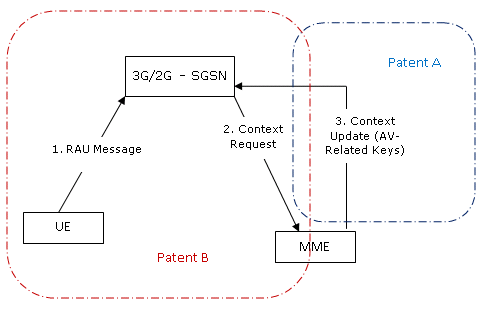
Now, we had two references which could be used together, in order to make the invention obvious to the person skilled in the art. But wait! That wasn’t the end. The use of references under clause ‘Obvious to the person skilled in the art’ is relative and may not be accepted by an examiner in the same way.
Therefore, we kept looking and sometime later, located a couple of prior art where these documents were cited together to show the link between them.
Voila, Mission accomplished.